Trojan Horse Generic17.AMPT is nasty computer threat which automatically enters your Windows PC without any consent. Your AVG will keep alerting you with popup at low right corner of your screen over and over again at each minute, making your system slow and crash. Usually Trojan Horse Generic17.AMPT makes use of the social network accounts (Facebook, Twitter, MSN, etc.) to expand its influence. It alters the settings, so that the hijacked accounts will send malicious links to associated users. Once infected, Trojan Horse Generic17.AMPT can trigger a series of terrible problems, such as BSOD, freezes, system errors, crashes and Internet connection failure. If you ignore these problems and don’t take immediate action to fix them, your PC may completely break down in a short period. What’s more, as a typical Trojan virus, Trojan Horse Generic17.AMPT is used by hackers to steal data from the infected PC, which means all your privacy is seriously endangered by this Trojan virus, and hackers also can access your system via the vulnerabilities created by Trojan Horse Generic17.AMPT virus. It is a really risky infection, and in order to prevent greater damage, it is recommended to remove Trojan Horse Generic17.AMPT as soon as possible.
Wednesday, April 30, 2014
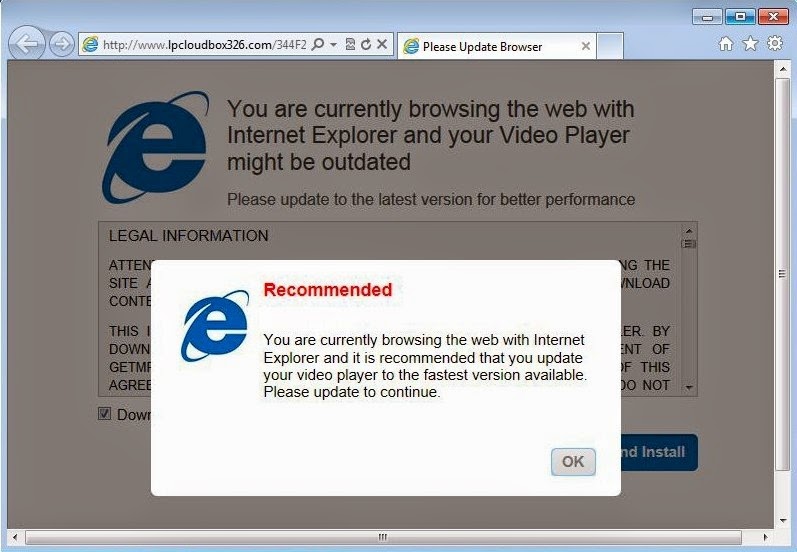
How to Remove lpcloudbox326.com - Guide to Get Rid of lpcloudbox326.com Easily
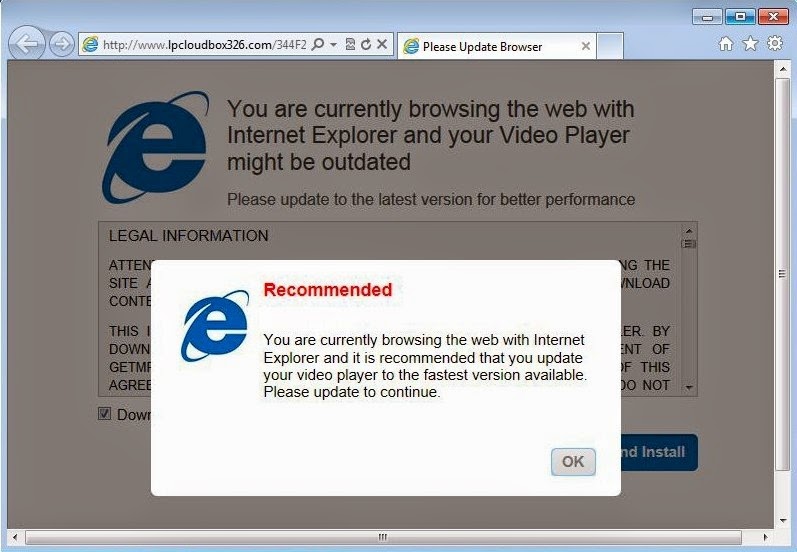
lpcloudbox326.com is a notorious browser hijacker redirection virus which will alter your homepage and slow down your computer’s performance. It is competent in dropping other malicious components like malware or Trojan horses onto the affected machine so as to produce further damage for the victims. Once the lpcloudbox326.com runs through you system, can also destroy your network and delete some critical files. It can do more except acting irritating. It can corrupt your PC like disabling your system registry and destroying computer files. lpcloudbox326.com also can collect your personal details as well as financial details without your knowledge and makes benefits from it. Most of the people go through browsing malicious webpages through their computers which are completely contained with various malicious agents which enters the PC while browsing, and make various unintentional changes in the system settings, browser settings, and Windows Registry settings. Since these settings in computers are essential to run the PC efficiently, if something goes wrong with them, it’s obvious for system get infected with lpcloudbox326.com. So, if you have seen this redirect virus on your computer, then it is very much advised that you remove lpcloudbox326.com from your computer system immediately.
Monday, April 28, 2014
How to Completely Get Rid of static.onlinefastpaydayloan.com popup (Step-by-Step Instructions)
static.onlinefastpaydayloan.com popup is a browser hijacker that can be added to Internet Explorer, Mozilla Firefox or Google Chrome without computer users’ knowledge and that tries to implement its malicious plans of generating numerous ads and distributing potentially unwanted programs.You may not be able to access any of the computer utilities like Task Manager, Registry Editor or others, as all of them might be deactivated. It is shaped so cleverly that it could simply dig out the loopholes in your computer system.
If your system has already been infected, you will be constantly receiving static.onlinefastpaydayloan.com popup offering you to update your Java or other legitimate program. However, if you follow what this message says you will actually agree to download a completely different program. This malware will flood your system with unwanted ads, fake update messages and redirect you to unwanted websites or even install other unwanted programs without your permission. Additionally, it can track your browsing history and record the information about your search queries. As a result, you may receive more targeted ads in future and you may be involved into other projects by the third parties.
static.onlinefastpaydayloan.com popup makes path for the other harmful malware or threats to get into the computer system and exploit it ruthlessly. It slows down the performance of the computer regularly and also hinders Internet accessibility in an improved manner. You will find it hard to use your computer system resources entirely as they were exceedingly confronted by the irritating windows system threats. In fact your important functionalities or other traits related to the system will also be disabled automatically. So, it is recommended to remove static.onlinefastpaydayloan.com popup from computer system as quick it is noticed.
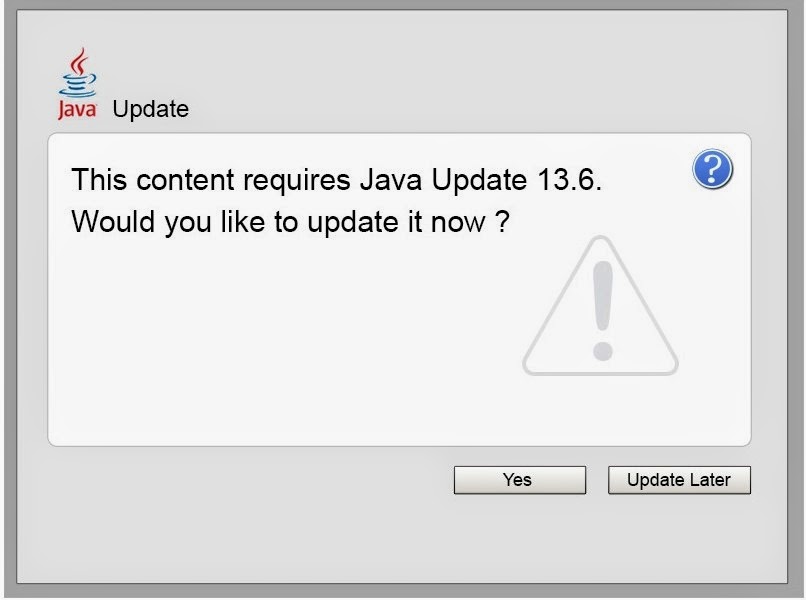
If your system has already been infected, you will be constantly receiving static.onlinefastpaydayloan.com popup offering you to update your Java or other legitimate program. However, if you follow what this message says you will actually agree to download a completely different program. This malware will flood your system with unwanted ads, fake update messages and redirect you to unwanted websites or even install other unwanted programs without your permission. Additionally, it can track your browsing history and record the information about your search queries. As a result, you may receive more targeted ads in future and you may be involved into other projects by the third parties.
static.onlinefastpaydayloan.com popup makes path for the other harmful malware or threats to get into the computer system and exploit it ruthlessly. It slows down the performance of the computer regularly and also hinders Internet accessibility in an improved manner. You will find it hard to use your computer system resources entirely as they were exceedingly confronted by the irritating windows system threats. In fact your important functionalities or other traits related to the system will also be disabled automatically. So, it is recommended to remove static.onlinefastpaydayloan.com popup from computer system as quick it is noticed.
Saturday, April 26, 2014
How to Remove alertfunctions.com Thoroughly: Manual Removal Method
alertfunctions.com a browser hijacker that installs into your computer from unethical way. It is designed to affect almost all browsers including Internet Explorer, Mozilla Firefox and Google Chrome. Once infected, alertfunctions.com is capable of collecting your browsers activity and sends it to remote server promoting related and unwanted ads. Every time you open your browsers, this redirect virus will lead you to the websites associated with this chain. You may not be able to employ any of the computer system tools like Task Manager, Registry Editor or others, as all of them might be deactivated. Moreover, alertfunctions.com also makes path for the other harmful malware or threats to get into the computer system and exploit it ruthlessly. It slows down the performance of the computer regularly and also hinders Internet accessibility in an improved manner. You will find it hard to use your computer system resources entirely as they were exceedingly confronted by the irritating windows system threats. In fact your important functionalities or other traits related to the system will also be disabled automatically. Thus, it is necessary to remove alertfunctions.com and remove its corrupt configurations from your browser.


Friday, April 25, 2014
Is Mostshinstar.com Malware? How to Remove Mostshinstar.com Manually?
 Mostshinstar.com is a nuisance redirect infection that can silently get attached to Firefox, Chrome or Internet explorer, once installed, this virus will hijack your web browser. In this situation, your homepage and search results or clicking on a web link while surfing the web will redirect you to Mostshinstar.com. This redirect virus will disable the genuine antivirus and any security program enters in your computer system or its block your access to any security related websites. Additionally Mostshinstar.com will remove your files on your hard disk and they disturb the innocent user to redirects their personal works through a malicious links. It forces victims to visit some vicious web pages when they visit these fraudulent links and misleading search results. It installs a variety of viruses on the compromised computer. Moreover, the producer of Mostshinstar.com gains money from hacked internet traffic. It is highly recommended that you remove Mostshinstar.com as soon as possible.
Mostshinstar.com is a nuisance redirect infection that can silently get attached to Firefox, Chrome or Internet explorer, once installed, this virus will hijack your web browser. In this situation, your homepage and search results or clicking on a web link while surfing the web will redirect you to Mostshinstar.com. This redirect virus will disable the genuine antivirus and any security program enters in your computer system or its block your access to any security related websites. Additionally Mostshinstar.com will remove your files on your hard disk and they disturb the innocent user to redirects their personal works through a malicious links. It forces victims to visit some vicious web pages when they visit these fraudulent links and misleading search results. It installs a variety of viruses on the compromised computer. Moreover, the producer of Mostshinstar.com gains money from hacked internet traffic. It is highly recommended that you remove Mostshinstar.com as soon as possible.Thursday, April 24, 2014
Cannot Uninstall ShopSave.Me - ShopSave.Me Virus Manual Removal
ShopSave.Me has been identified as an adware, which is able to interrupt your browsers when you surf on the Internet. This hazardous adware can infiltrate into its target machines via suspicious websites, spam emails, and other unsafe downloads. It silently gets installed on popular browsers like Chrome, Firefox, IE, etc. Just like other malwares, this one is also used for recommending users discounts. But apart from this, the adware will an extra ordinary infection which keeps record of your browsing habits and collects your personal information which is later on sent to hackers. After ShopSave.Me is installed on your system, something strange will happen frequently. This annoying adware will change the default settings of the registry entries, DNS and the browser. As a result, ShopSave.Me is able to boot up automatically and replace your homepage without approval. Moreover, there will be more and more annoying ads popping up on the screen when you surf the Internet. What really drives you crazy is that this adware will always take up more and more RAM, and then your PC will run slowly as snail. To solve those serious problems, you should remove ShopSave.Me from the system in time.


How to Completely Get Rid of Adware generic_r.KF (Step-by-Step Instructions)
Adware generic_r.KF or Adware generic_r.KG is an adware that hijacks internet browsers and modifies important settings which causes web redirection problems. It displays advertisements within your browser and Flash update boxes with the sole purpose of generating revenue for the cyber criminals. It will disable your browser security and distribute as many threats as possible onto your computer without any permission. Adware generic_r.KF tries tracking your browsing habits and getting some information about what pages you are visiting and what information you are browsing about on the Internet. Such data can be very valuable for marketing companies. Moreover, it may turn out that without your knowledge your computer has become an object of attacks of PC viruses, worms, and malware infections. The aim of hackers is to gain access to your PC and steal your information and money. Hackers will have free access to your log in details, user names, passwords, bank account information and browsing history. Without your knowledge, you will become a victim of credit card and identity theft. Cyber criminals will be able to use all your details for personal purposes. Therefore, it is important not to waste time to remove Adware generic_r.KF from your PC.
Tuesday, April 22, 2014
How to remove Dm.startnow.com from Infected PC? ( Effective Removal Guides)
Dm.startnow.com is a browser hijacker which is designed to promote their search engines and homepage. It hijacks your browser regardless of Internet Explorer, Mozilla Firefox and Google Chrome and exhibits numerous malicious exhibits. It usually gets into your computer when you visit suspicious sites, open junk e-mails, or download free programs from unknown resources. Once Dm.startnow.com intrudes in your operating system successfully, it will add malicious files to the system registry. Then numerous ads would be displayed on the screen during your web browser activities. Some of the ads may induce you to buy some promoted products while some might contain unknown viruses. Dm.startnow.com provides you with irrelevant and useless search results. Besides, your new tabs could be redirected to unneeded websites as well. It may affect your computer’s speed by deleting entries in the registry and other important operating system files. This redirect infection is used for spying targeted computer to record and steal personal user information which can be utilized for marketing or other criminal purposes. Hence, for the safety of your computer, do not hesitate to remove Dm.startnow.com as fast as you can.


Monday, April 21, 2014
How to Remove W32.Mezit!inf - W32.Mezit!inf Manual Removal
 W32.Mezit!inf is a very dangerous Trojan virus which is created by web criminals to cause damage to the affected computer and steal sensitive information from the victim. It is reported that this risky virus is spread on the Internet wildly and furtively through spam e-mail attachments, suspicious websites, and unknown free resources like programs and files, and so forth. After successful intrusion, W32.Mezit!inf virus will distribute its clones to some major system parts so as to take over the whole Windows. It injects start-up files to the system registry. Besides, this pest is able to change the computer security settings to cause malfunctions to the installed antivirus and anti-spyware. W32.Mezit!inf virus keeps changing its traits, which makes it more difficult to completely remove this bug. The worst is that this nasty Trojan allows the distant hackers to access the system and take away your crucial information that is stored on the machine. That will be a great danger for your privacy. Thus, it is an urgent an necessary to remove W32.Mezit!inf virus completely.
W32.Mezit!inf is a very dangerous Trojan virus which is created by web criminals to cause damage to the affected computer and steal sensitive information from the victim. It is reported that this risky virus is spread on the Internet wildly and furtively through spam e-mail attachments, suspicious websites, and unknown free resources like programs and files, and so forth. After successful intrusion, W32.Mezit!inf virus will distribute its clones to some major system parts so as to take over the whole Windows. It injects start-up files to the system registry. Besides, this pest is able to change the computer security settings to cause malfunctions to the installed antivirus and anti-spyware. W32.Mezit!inf virus keeps changing its traits, which makes it more difficult to completely remove this bug. The worst is that this nasty Trojan allows the distant hackers to access the system and take away your crucial information that is stored on the machine. That will be a great danger for your privacy. Thus, it is an urgent an necessary to remove W32.Mezit!inf virus completely.Saturday, April 19, 2014
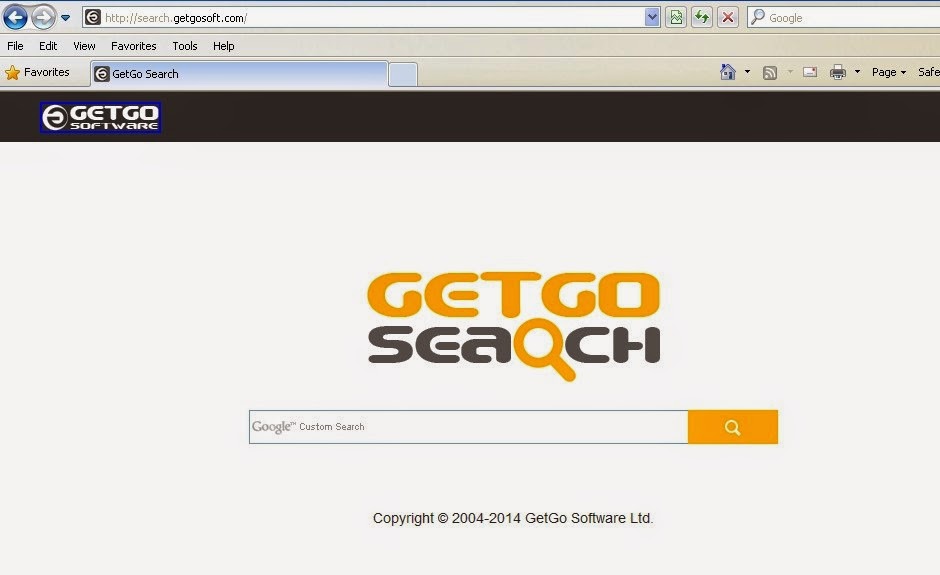
How to Get Rid of Search.getgosoft.com (Manual Removal Guide)
Search.getgosoft.com, also known as GetGo Search, is a released redirect virus or browser hijacker that attacks all internet browsers including Google Chrome, IE and Firefox, etc. Generally speaking, this virus is spread via spam e-mails, corrupt websites, pirated movie torrents and other unsafe downloads. When you open those unsafe files, Search.getgosoft.com will quickly sneak into and finish the installation. Once infected, it has the ability to change the browser settings including default search engine, homepage and privacy settings to take the complete control of your browser. It has the ability to modify the existing registry entries, and create the new corrupt entries so that it can start itself every time you open the windows. Moreover, Search.getgosoft.com has the ability to change the security settings by disabling the antivirus program installed in your computer due to which the system becomes vulnerable to the other similar threats. This redirect virus is actually designed to steal your personal as well as financial information to use it for fraud purpose. Once this tricky virus detected in your computer, you need to get rid of this quickly by using the following manual removal method.
How to Completely Remove Trojan.Zekos.Patched from Infected System, Virus Removal Help
 Trojan.Zekos.Patched is classified to be a tricky Trojan horse virus, which can invade your PC and cause a great duel of damage to the security system. It is made by cyber criminals who want to gain benefit from victims. If you are infected by Trojan.Zekos.Patched, it sneaks into your PC system and modifies your registry. Your browser will be hijacked to some other malicious pages. Gradually, your system will run lower than before and often end up with crash. Besides, Trojan.Zekos.Patched may download a ransomware to lock up your desktop so that you can do nothing with your machine. However, though you are really upset about this Trojan virus, you cannot get rid of it completely by normal antivirus programs because this virus can hide deep inside the system and change its location frequently. Meanwhile, Trojan.Zekos.Patched has the ability to open backdoor for the hackers. Then, the hackers can break into your system easily to steal your important information like credit card number. So Trojan.Zekos.Patched is a danger to your PC, and you should get rid of it without hesitation.
Trojan.Zekos.Patched is classified to be a tricky Trojan horse virus, which can invade your PC and cause a great duel of damage to the security system. It is made by cyber criminals who want to gain benefit from victims. If you are infected by Trojan.Zekos.Patched, it sneaks into your PC system and modifies your registry. Your browser will be hijacked to some other malicious pages. Gradually, your system will run lower than before and often end up with crash. Besides, Trojan.Zekos.Patched may download a ransomware to lock up your desktop so that you can do nothing with your machine. However, though you are really upset about this Trojan virus, you cannot get rid of it completely by normal antivirus programs because this virus can hide deep inside the system and change its location frequently. Meanwhile, Trojan.Zekos.Patched has the ability to open backdoor for the hackers. Then, the hackers can break into your system easily to steal your important information like credit card number. So Trojan.Zekos.Patched is a danger to your PC, and you should get rid of it without hesitation.Friday, April 18, 2014
Remove Canadaaltax.com Virus (Step-by-Step Removal Instructions)
Canadaaltax.com is a dangerous browser hijacker that created by web criminals to take the control of your Google Chrome, Internet Explorer and Mozilla Firefox via modifying the default browser settings. It can enter your computer when you visit any hacked website, download a certain free program, and click any contaminated link or icon. Canadaaltax.com has the ability to bypass antivirus and infiltrate the target operating system. Once infected, it has ability to alter both your original start page and your favourite search engine. As result, you will get lots of redirects of your visits to certain misleading websites. Canadaaltax.com restricts PC users from normal Internet surfing because they are continuously represented with various offers and rerouted to doubtful commercial websites. It is able to substitute the default start page and search provider or open its website as a new tab page. Moreover, it is able to obtain information about the computer users’ surfing habits, to gather their privacy. It records what websites the computer user is visiting, usernames, passwords and other private details to use this data for marketing campaigns. Thus, it is highly advised to remove Canadaaltax.com to protect the PC as well as your privacy.
How to Remove WebSearch.com Thoroughly: Manual Removal Method
WebSearch.com is a vicious browser hijacker or redirect virus which aims to load on web browser programs as homepage or search engine. It usually comes into your computer with spam email attachments, unsafe websites or unverified downloads, etc. once your computer is affected by WebSearch.com, you will encounter lots of popups. It attacks popular Internet browsers like Internet Explorer, Google Chrome and Mozilla Firefox. These browsers will be redirected to unwanted sites at random times. Through the infected computer users will notice the WebSearch.com being loaded where they are forced into using the page as their search engine site choice instead of others like Google, yahoo or Bing. Moreover, the existence of WebSearch.com virus is a huge threat to your privacy, because this virus has the ability to collect victims’ private data from monitoring browsing processes. All your surfing activities are monitored by WebSearch.com, which means the virus can steal your private data and transmit the records to remote hackers. Therefore, in addition to PC problems, you are likely to encounter financial losses, data missing or other severe consequences. Hence, in order to avoid the more damage, it is important to remove WebSearch.com as quickly as possible.
Thursday, April 17, 2014
Remove JW video player pop up (Uninstall Guide)
Every time I load a YouTube video, a JW player ad pops up. It's annoying and opens ad when I click on it. Where did it come from? How can I stop it? It opens various ads saying that my Flash Player is out of date and to upgrade, but the URL isn't from adobe, it's a random string of numbers and letters. My pop-up blocker isn't catching anything, and it interupts whatever I'm doing with a windows box warning me about an out of date Flash Player. How can I stop this? I have no viruses, and it's on IE, Firefox and Torch. And when I click on a new webpage, an ad, "Mash Buttons" pops up, no matter the website! Once again, my ad-blocker doesn't say anything.
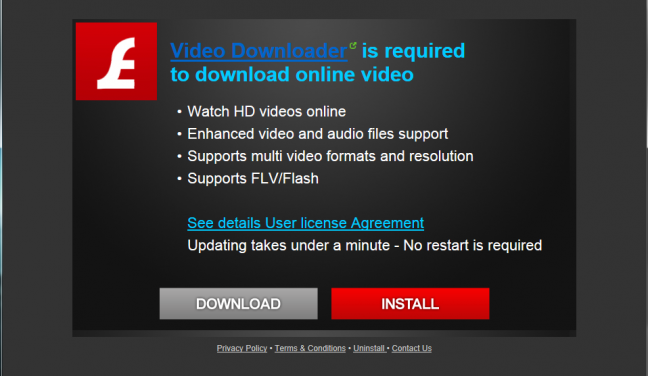
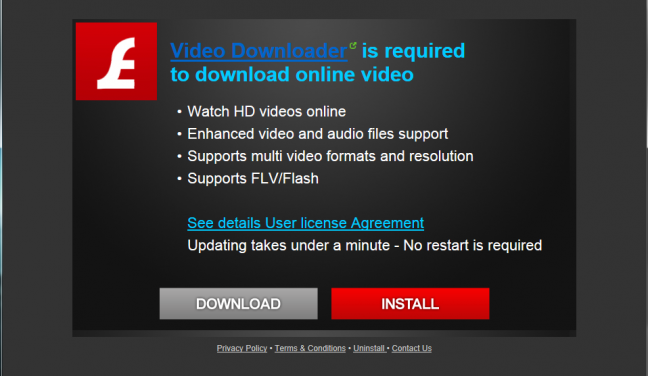
JW video player pop up is a potentially unwanted program that can be attached as a unwanted extension with Firefox, Safari, Chrome, etc web browsers to change their default homepage, DNS settings and security configurations. Once your system has been affected by JW video player pop up invasion, your homepage and default search engine will be replaced with JW video player. Once install on a computer, the JW video player will display pop-up ads within your browser and Flash update boxes with the sole purpose of generating revenue for the cyber criminals.
Remove Cr.tractionize - Completely Delete and Get Rid of Cr.tractionize
Cr.tractionize is categorized as a browser hijacker which could cause serious damages to your computer. It is distributed through several means. Malicious websites, or legitimate websites that have been compromised, may drop this Trojan onto a compromised computer. It will hijack your browser, displays annoying commercials that will keep popping up on your screen. After successfully enter into your PC, Cr.tractionize will show you lots of pop ups messages and fake warning messages. Sponsored links will also be flashed on your screen and it may take you to some particular sites or to the hub of infections. It acts like an adware infection which means it generates tons of pop-up advertisements and reroutes your online requirements to ads-related websites. Via this way, its creator can benefit a lot from the increased online traffic. What’s worse, Cr.tractionize will sneak into the computer system and open a backdoor on your computer that allows attackers to access and steal crucial data; delete important files and initiate additional attacks on the computer system and network that you use. Additionally, it drops lots of malicious codes into the computer which disturb user at working time. So it can turn out to be the loophole that utilized by cybercriminal to come and steal personal information away. Therefore it is very important to remove Cr.tractionize as soon as possible.
Wednesday, April 16, 2014
Learn to Remove Dos/Rovnix.gg Step by Step (Virus Removal)
 Dos/Rovnix.gg is a destructive Trojan horse which reported by Windows Security Essentials even immediately after cleaning it. It affects your security programs like firewall and antivirus software. It inserts its malicious codes throughout the compromised Operating System; it creates numerous executable and registry keys so that it gets really complicated to intercept and disable its functioning. Moreover, this Trojan virus communicates with the distant hackers to do constant update. So this nasty virus changes its traits to make it hard to remove. What is more, Dos/Rovnix.gg virus can introduce additional dangerous viruses including worms, spyware, adware, browser hijackers and malware. Under such circumstance, you will encounter a chaotic workstation while the Windows will be definitely damaged. The worst is that Dos/Rovnix.gg virus can manipulate your keystrokes and online activities to collect sensitive information for its designers. That will be really dangerous for your privacy and finance. Thus, it is recommended to remove Dos/Rovnix.gg virus to protect your computer.
Dos/Rovnix.gg is a destructive Trojan horse which reported by Windows Security Essentials even immediately after cleaning it. It affects your security programs like firewall and antivirus software. It inserts its malicious codes throughout the compromised Operating System; it creates numerous executable and registry keys so that it gets really complicated to intercept and disable its functioning. Moreover, this Trojan virus communicates with the distant hackers to do constant update. So this nasty virus changes its traits to make it hard to remove. What is more, Dos/Rovnix.gg virus can introduce additional dangerous viruses including worms, spyware, adware, browser hijackers and malware. Under such circumstance, you will encounter a chaotic workstation while the Windows will be definitely damaged. The worst is that Dos/Rovnix.gg virus can manipulate your keystrokes and online activities to collect sensitive information for its designers. That will be really dangerous for your privacy and finance. Thus, it is recommended to remove Dos/Rovnix.gg virus to protect your computer.Removal Guide - How to Remove police-warning-alert.com Easily and Permanently?
police-warning-alert.com is a very dangerous infection that severely infects Windows PC and MAC X OS. It is new variant from the MoneyPak virus family to require payment to unlock your browsers. It mainly attacks some popular Internet browsers such as Google Chrome, Internet Explorer, Mozilla Firefox and Safari. Once it is installed in your PC, you will see that there is a scary warning message stating your computer has been suspended on the grounds of unauthorized cyber activity. Because violations of the law such as distribution of pornographic files, visit the websites of terrorist groups, distribution of virus programs, etc. police-warning-alert.com can hurt your critical documents or reveal your own personal details like your ID, name, telephone numbers, address and post signal to cyber-criminal for their use criminal intent. It may bring further infections are direct the user to infectious sites. Tee Support experts suggest that police-warning-alert.com should be cleaned up from the affected machine as fast as possible. police-warning-alert.com has a remote link with the associated hackers to grant them the permission to take full control over the infected system. These hackers with the help of keyloggers trace your web history and keeps record of activities in order to trap you for their illicit motive. It can block your web activities by hijacking browsers and even disables your browsers. To be worse, it manages to steal information like user name, password or other useful credentials of innocent user's. Therefore, it is highly needed that you should immediately remove police-warning-alert.com as soon as possible before it bring more damage to your security and privacy.
Monday, April 14, 2014
Remove SavePass Thoroughly - Ads by SavePass Manual Removal Method
SavePass(aka Ads by SavePass) is a Potentially Unwanted Program or adware because it inflicts and acts as a malicious threat into your computer system. It can change default settings without permission. It invades into your system when you visit suspicious websites, click malicious links or download unverified free programs, etc. Once SavePass infiltrates your PC successfully, it has ability to change the default home page or web browser search engine automatically. It redirects web search queries to unwanted sites or manipulated results. It will hijack your web browsers such as Google Chrome, Internet Explorer and Mozilla Firefox to set itself as your default homepage and search engine. And then there will be with lots of irrelevant and sponsored links instead of useful and informative search results. Moreover, SavePass causes a lot of web redirects to promoted web pages with lots of floating ads and commercial products. If you accidentally click any of the offered links, you would be led to the installation of additional risky viruses like Trojans. What’s more, this kind of adware monitors your keystrokes and gathers your important information. Then the collected data will be sold to some web criminals for illegal purposes like carrying out commercial activities or delivering spam emails. Therefore, it is necessary to remove SavePass immediately to keep a safety network on your computer.
Saturday, April 12, 2014
Virus Removal Guide - How to Completely Get Rid of POSHCODER Malware From infected PC?
 POSHCODER Malware (aka .poshcoder files) is a newly encrypted virus that encrypts important files and makes your computer system or network completely disable. The infection makes security vulnerable then break into the infected computer. This malware represents security risk for the compromised system and its network environment. Once .poshcoder files nasty threat gets installed, the files on desktop and drive files will be encrypted with .poshcoder files. It leaves one Unblock Files.vbs in each folder where it encrypted the files. To trick victims’ money, .poshcoder files decrypted one file for me, and for the rest it is asking bitcoins to be added to one of the wallet. However, you’d better not to support its online fraud, for there may be no use to pay for cyber hackers. It is highly recommended that you remove POSHCODER Malware before more damages to your system.
POSHCODER Malware (aka .poshcoder files) is a newly encrypted virus that encrypts important files and makes your computer system or network completely disable. The infection makes security vulnerable then break into the infected computer. This malware represents security risk for the compromised system and its network environment. Once .poshcoder files nasty threat gets installed, the files on desktop and drive files will be encrypted with .poshcoder files. It leaves one Unblock Files.vbs in each folder where it encrypted the files. To trick victims’ money, .poshcoder files decrypted one file for me, and for the rest it is asking bitcoins to be added to one of the wallet. However, you’d better not to support its online fraud, for there may be no use to pay for cyber hackers. It is highly recommended that you remove POSHCODER Malware before more damages to your system.Best Way to Remove AdChoices, Easily and Permanently
AdChoices (also known as Ad Choices) is an adware which is developed by hijacker to infect all the user’s browsers including the Internet Explorer, Google Chrome and Mozilla Firefox, etc. Once this malware gets into the computer system and exploit it ruthlessly. It slows down the performance of the computer regularly. When the PC user attempts to look for anything on the net in any genuine search provider, he may see AdChoices on the browser that may show a variety of pop-up adverts and sponsored links associated with the computer user’s browsing habits. It may trace the PC user’s surfing activity and transmit collected data to third-parties for unknown intentions. You can see that the browser performs poorly, which is often hijacked to AdChoices. It displays unstoppable pop-up advertisements on your screen, every time you visit shopping or social websites. Besides, this adware is able to spread itself with your MSN, Twitter and Facebook accounts, which means that it will send malicious messages to your friends automatically. AdChoices may consume all resources making the system performance and internet connection extremely slow. It can takes over the infected web browser and leads to annoying diversions to doubtful web pages. It can completely invade a computer in hidden form without even making the user recognize it. This threat may hidden or delete your files such as MS Office documents, videos, images, music and etc. So, for the safety of your personal information, it is necessary to remove AdChoices from the system immediately.
Friday, April 11, 2014
Effective Guide to Remove Name Not Available Virus - Manually Removed
Today my computer restarted randomly and when it turned back on, every time I opened IE, the computer starts playing random collections of advertisements in the background. I can mute the specific problem in my volume mixer for the speakers and it was titled "Name Not Available". I ran a Norton 360 scan and a Malwarebytes scans and nothing was discovered.
While I'm not sure what happened, my parents computer has a virus, and now random ads, and sometimes music play in the background (no... IE, FF, Chrome, Safari, Opera, whatever are all closed). This happens on start-up, so I'm sure a hidden open program. If I pull up the Sound Mixer, I can see it under the application, but it is listed as "Name Not Available" I've run Malwarebytes, Avira, Spybot S&D, and SuperAntiMalware, however I cannot seem to get rid of it.
Last night I turned on my moms laptop and after it connected to WiFi, what sounded like a radio station came on, without Google Chrome or Internet Explorer being open. I opened the Audio Mixer, and there was a program that was running in it. It said "Name not available". I looked up this problem and found out that this could possibly be a root kit. I worked for about 8-10 hours on this laptop trying to get this off. I have ran Malwarebytes, Avira, Windows Defender(all full scans). I have also used Rouge Killer, TDSS Killer, Security Check, ADWcleaner, Combo fix, Hijack this, Hitman pro, Emsisoft Emergency kit, Junkware Removal tool, and Spybot Search and Destroy. NOTHING WORKS. This is my last resort. I need an expert.
I don't exactly know when it started, but every time I start up my computer and go into the mixer there is a source titled Name not available. It's muted and you can't unmute it. If you mess around with the slider you can sometimes get sound to come in, and it sounds like a radio that keeps changing stations. The only way to stop it is to disable the internet and then it stops, but once I re-enable the internet it starts back up again. I have no clue what it is and what its coming from. I've ran multiple virus and malware scans on my computer with a bunch of different programs and they have found nothing. It also severely impacts my internet speed. I have scanned through the task manager processes and services, and didn't find anything.
Name Not Available Virus is a malicious malware infection which is designed by cyber criminals with illicit aim to generate commission by fooling the innocent users. Basically, Name Not Available is caused by an attack from a Trojan horse virus on the audio driver. Once infected, you can see a "Name not available" channel for the audio ads being created in my Volume Mixer. This malware performs dangerous activities to harm the PC severely, and computer users may hear strange replicated sounds in the machine. Computer users may hear weird constant sounds in the system background every time they start the computer. Distinguished from other common virus, Name Not Available threat will not reproduce by itself and intentionally infect other documents. Apart from strange sounds, many random ads pop up from time to time. Once intruding, Name Not Available will do lots of harmful activities on your computer, such as monitor traffic and keystrokes; create a "backdoor" into the system for the hacker's use; alter log files; attack other machines on the network; and alter existing system tools to escape detection. Name Not Available can also escape from many antivirus or security applications and has the ability to hide connections, files and process. Considering the safety of your computer, it’s highly recommended to remove Name Not Available completely from your system as soon as possible.
While I'm not sure what happened, my parents computer has a virus, and now random ads, and sometimes music play in the background (no... IE, FF, Chrome, Safari, Opera, whatever are all closed). This happens on start-up, so I'm sure a hidden open program. If I pull up the Sound Mixer, I can see it under the application, but it is listed as "Name Not Available" I've run Malwarebytes, Avira, Spybot S&D, and SuperAntiMalware, however I cannot seem to get rid of it.
Last night I turned on my moms laptop and after it connected to WiFi, what sounded like a radio station came on, without Google Chrome or Internet Explorer being open. I opened the Audio Mixer, and there was a program that was running in it. It said "Name not available". I looked up this problem and found out that this could possibly be a root kit. I worked for about 8-10 hours on this laptop trying to get this off. I have ran Malwarebytes, Avira, Windows Defender(all full scans). I have also used Rouge Killer, TDSS Killer, Security Check, ADWcleaner, Combo fix, Hijack this, Hitman pro, Emsisoft Emergency kit, Junkware Removal tool, and Spybot Search and Destroy. NOTHING WORKS. This is my last resort. I need an expert.
I don't exactly know when it started, but every time I start up my computer and go into the mixer there is a source titled Name not available. It's muted and you can't unmute it. If you mess around with the slider you can sometimes get sound to come in, and it sounds like a radio that keeps changing stations. The only way to stop it is to disable the internet and then it stops, but once I re-enable the internet it starts back up again. I have no clue what it is and what its coming from. I've ran multiple virus and malware scans on my computer with a bunch of different programs and they have found nothing. It also severely impacts my internet speed. I have scanned through the task manager processes and services, and didn't find anything.
Name Not Available Virus is a malicious malware infection which is designed by cyber criminals with illicit aim to generate commission by fooling the innocent users. Basically, Name Not Available is caused by an attack from a Trojan horse virus on the audio driver. Once infected, you can see a "Name not available" channel for the audio ads being created in my Volume Mixer. This malware performs dangerous activities to harm the PC severely, and computer users may hear strange replicated sounds in the machine. Computer users may hear weird constant sounds in the system background every time they start the computer. Distinguished from other common virus, Name Not Available threat will not reproduce by itself and intentionally infect other documents. Apart from strange sounds, many random ads pop up from time to time. Once intruding, Name Not Available will do lots of harmful activities on your computer, such as monitor traffic and keystrokes; create a "backdoor" into the system for the hacker's use; alter log files; attack other machines on the network; and alter existing system tools to escape detection. Name Not Available can also escape from many antivirus or security applications and has the ability to hide connections, files and process. Considering the safety of your computer, it’s highly recommended to remove Name Not Available completely from your system as soon as possible.
Thursday, April 10, 2014
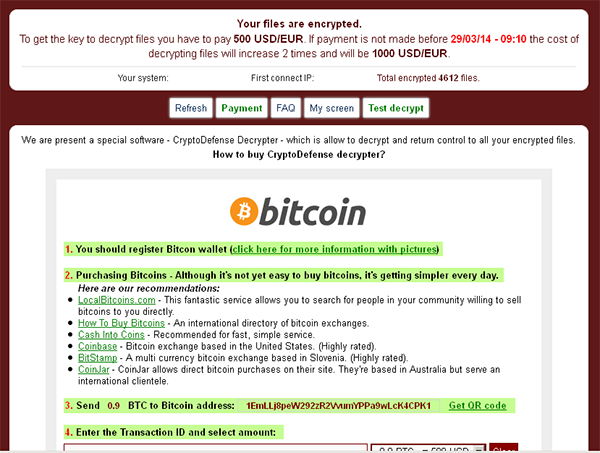
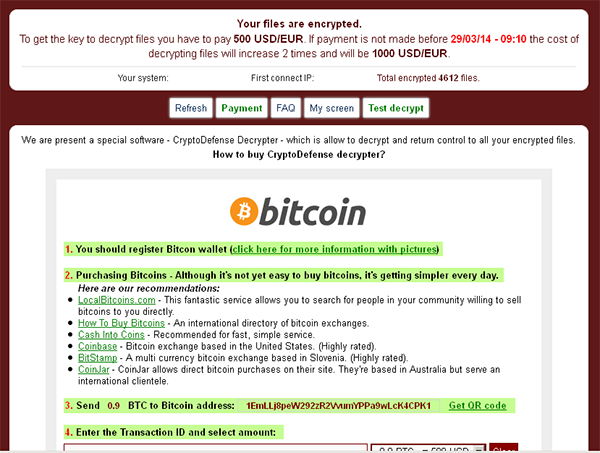
How to Completely Get Rid of CryptoDefense? - Efficient Manual Removal
CryptoDefense is a malicious malware categorized as ransomware that targets the operating system of Windows PC: Win XP, Win Vista, Win 7 or Win8. Similar to CryptoLocker, CryptorBit and HOWDECRYPT viruses, CryptoDefense Software virus or How Decrypt virus will encrypt certain files on the computer and demand payment before you can gain access to the said files. However, it seems that CryptoDefense demands higher than other ransomware. It demands user to pay 1000 USD/EUR through online payment scheme. Once infected, CryptoDefense states that "All files including videos, photos and documents on your computer are encrypted by CryptoDefense Software. Encryption was produced using a unique public key RSA-2048 generated for this computer. To decrypt files you need to obtain the private key. The single copy of the private key, which will allow you to decrypt the files, located on a secret server on the Internet; the server will destroy the key after a month. After that, nobody and never will be able to restore files. In order to decrypt the files, open your personal page on the site https://rj2bocejarqnpuhm.browsetor.com/1jt3 and follow the instructions. If https://rj2bocejarqnpuhm.browsetor.com/1jt3 is not opening, please follow the steps below: 1. You must download and install this browser http://www.torproject.org/projects/torbrowser.html.en 2. After installation, run the browser and enter the address: rj2bocejarqnpuhm.onion/1jt3 3. Follow the instructions on the web-site. We remind you that the sooner you do, the more chances are left to recover the files. IMPORTANT INFORMATION: Your Personal PAGE: https://rj2bocejarqnpuhm.browsetor.com/1jt3 Your Personal PAGE(using TorBrowser): rj2bocejarqnpuhm.onion/1jt3 Your Personal CODE(if you open site directly): 1jt3" However, whatever it changes, it is just a scam that wants to collect money and information from the victims. Never follow its instruction and finish payment, or you will lose your money and information on the infected machine, you must take action to get rid of this CryptoDefense as soon as possible to avoid further damage.
Tuesday, April 8, 2014
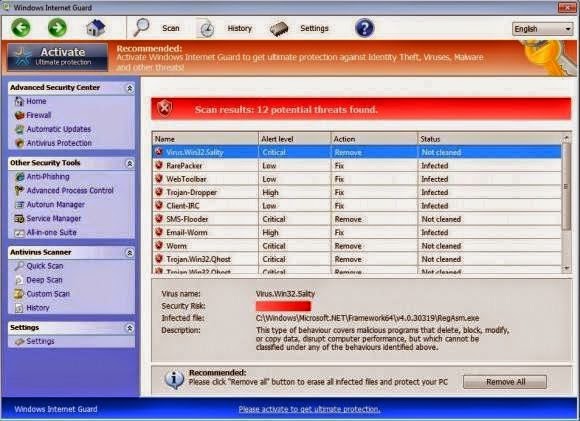
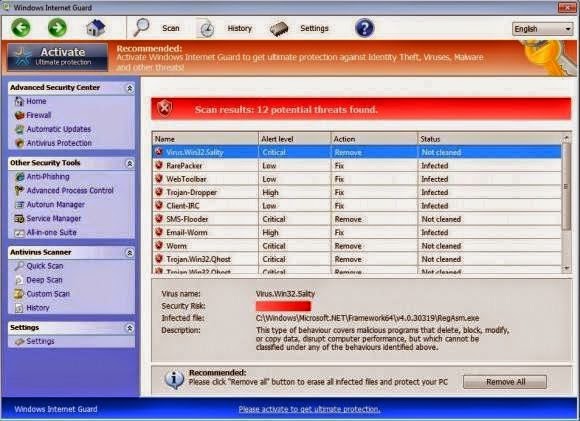
Remove Windows Internet Guard Thoroughly: Manual Removal Method
Windows Internet Guard is categorized as rogue antispyware which enters without any notification. This virus can attack a computer silently, it does not let the user notice of its installation, usually this type of infections are caused by Downloader Trojan from malicious websites or they come together with free-ware downloads. Once it executes it automatically scans your system and shows fake results. This infection floods your computer screen through lot of unwanted alerts. Windows Internet Guard acts as an anti-virus scanner, and it represents a report telling that Windows Internet Guard has detected viruses on your computer. If you click the "Continue" or REMOVE VIRUS or any similar link inside the Windows Internet Guard software, it will take you to the processes of buying full version of this program. It redirects the search results to the malicious sites. Actually it is not good for computer because it ruin the system when it gets installed. Apart from this it will collect your personal information including user names, email account, online transaction and transfer it to the cyber hacker. It will display may unwanted links and show lot of malicious activities while you are working on the computer. This infection infiltrates in to system with the help of Trojan virus. Due to this condition user faces many dangerous problems and the also unable to run any program into the Windows system. It is recommend you to remove Windows Internet Guard immediately.
How to Manually Remove Adware.SweetIM - Guide to Get Rid of Adware.SweetIM Easily
Adware.SweetIM is a stubborn adware infection that gets install in your system secretly. it may enter in you system when you clicked on any suspicious link or via downloading video files from Internet that time. Once it successfully enter in your system, it will very fast propagate itself in multiple copies and occupy more space in your system hard disk due to this your system performance will be slowdown automatically. It will change the DNS setting of your system and also turn off all important windows functionality. Adware.SweetIM floods your computer screen with number of fake and unwanted advertisements and sponsored link, and it makes the infected computer to run very slowly and weird. Moreover, it changes the default setting of the internet web browser of your computer and while surfing internet, this infection will redirect you to other links that are full of fake and malicious advertisements. This pest also damages Windows registry entries and system files that plays key role in smooth running of Windows system. For smooth running of user computer, it is necessary to remove Adware.SweetIM as soon as possible.


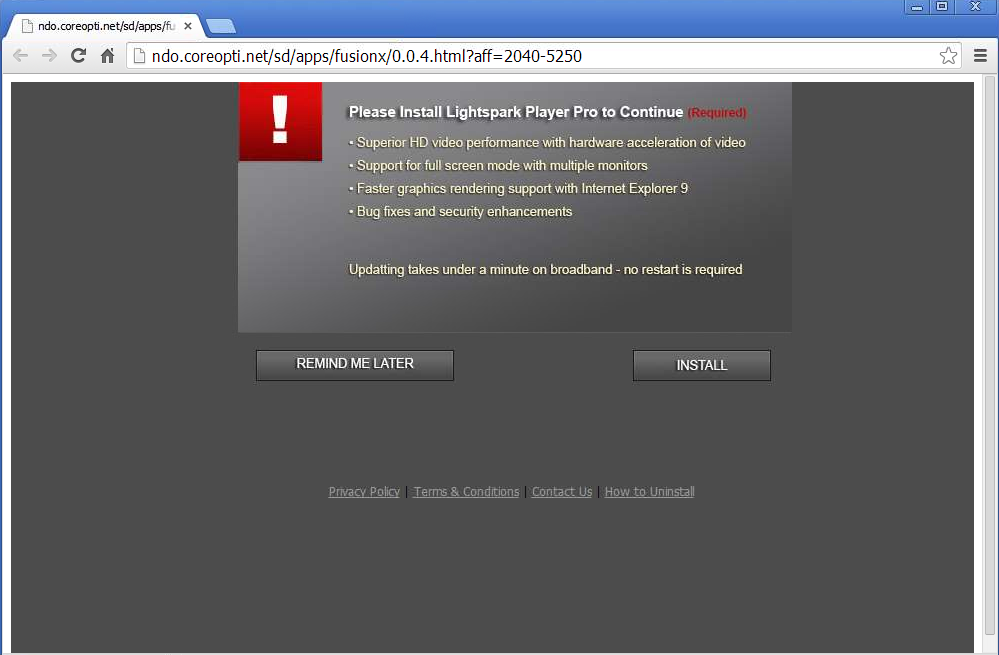
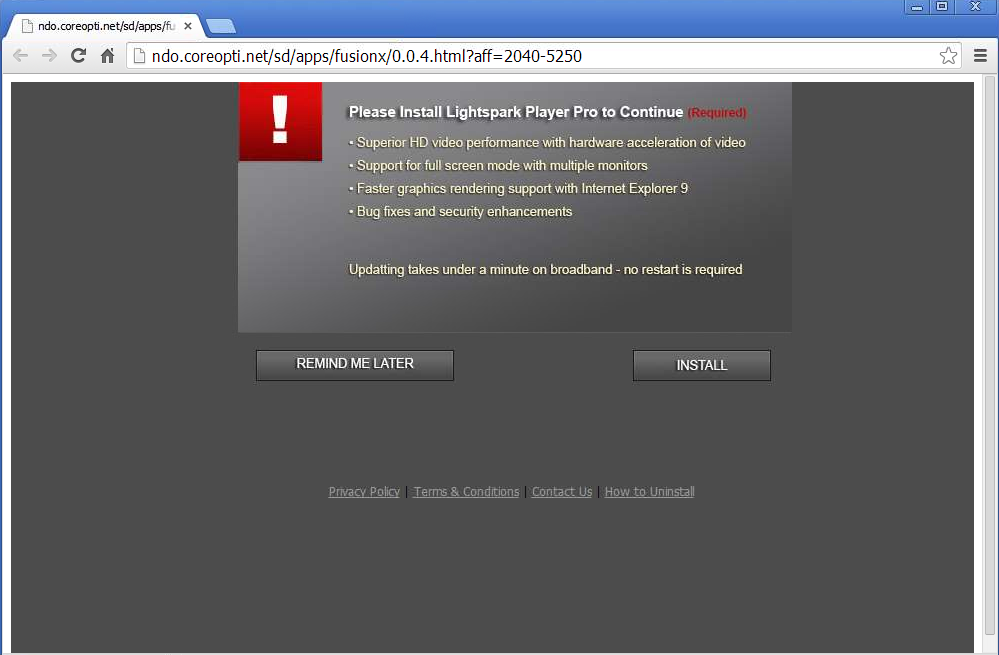
How to Remove ndo.coreopti.net Browser Hijacker Infection? (Virus Manual Removal Help)
ndo.coreopti.net is a malicious browser hijacker or redirect virus that is known for loading on web browser programs as a new set home page or search engine. It mainly attacks some popular Internet browsers such as Google Chrome, Internet Explorer and Mozilla Firefox, and these browsers will be redirected to unwanted sites at random times. Usually, Remote hackers can spread this adware or pop-up virus into your computer through spam e-mail attachments, unsafe websites or unverified downloads and so forth. Once it enters onto user’s PC, it modify or change user desktop settings as well as homepage and also display adds that will disturb PC users when they are working on the internet. ndo.coreopti.net is capable to perform any kind of malicious tasks on your machine such as install BHO on your web browser and it can easily monitor your online activities. In order to escape form the antivirus, it will delete some of your system files and modify your firewall settings. Moreover, ndo.coreopti.net may consume all resources making the system performance and internet connection extremely slow. It can takes over the infected web browser and leads to annoying diversions to doubtful web pages. It can completely invade a computer in hidden form without even making the user recognize it. This threat may hidden or delete your files such as MS Office documents, videos, images, music and etc. So, for the safety of your personal information, it is necessary to remove ndo.coreopti.net from the system immediately.
Friday, April 4, 2014
How to Remove Trojan:Win32/Lecpetex.A - Virus Manual Removal Guide
 Trojan:Win32/Lecpetex.A is a harmful Trojan horse which has a variety of malicious features to destroy the PC. Usually it attached the program that user get download from Internet and easily comes into your computer with the attachment of Spam emails, file sharing, social network sites and other nasty stuff from the malicious websites.This thread opens up a backdoor or port in the PC, fetches upgrades for itself and also uploads your private data through the same virtual hole to a remote server. Once you click the hyperlink without realization which system can be plummeted and fall into Trojan:Win32/Lecpetex.A. It disguises itself in the hidden folder of the windows system and once it got there it will be very difficult to be removed from your computer. it is destructive because it not only hampers your infected computer by itself, but also adds additional viruses to attack the compromised PC. Trojan:Win32/Lecpetex.A attacks all versions of Windows PC and gets installed on the host computer without any permission whatsoever. it strongly suggests you to check your system and remove Trojan:Win32/Lecpetex.A Trojan virus as soon as possible.
Trojan:Win32/Lecpetex.A is a harmful Trojan horse which has a variety of malicious features to destroy the PC. Usually it attached the program that user get download from Internet and easily comes into your computer with the attachment of Spam emails, file sharing, social network sites and other nasty stuff from the malicious websites.This thread opens up a backdoor or port in the PC, fetches upgrades for itself and also uploads your private data through the same virtual hole to a remote server. Once you click the hyperlink without realization which system can be plummeted and fall into Trojan:Win32/Lecpetex.A. It disguises itself in the hidden folder of the windows system and once it got there it will be very difficult to be removed from your computer. it is destructive because it not only hampers your infected computer by itself, but also adds additional viruses to attack the compromised PC. Trojan:Win32/Lecpetex.A attacks all versions of Windows PC and gets installed on the host computer without any permission whatsoever. it strongly suggests you to check your system and remove Trojan:Win32/Lecpetex.A Trojan virus as soon as possible.Tuesday, April 1, 2014
Virus Removal Guide - How to Completely Get Rid of Policeweblab.com From infected PC?
Policeweblab.com is a ransomware infection that created by cyber criminals to trace your personal and financial details before it has demonstrated its presence on your computer and it has locked your browsers like Internet Explorer, Google Chrome and Mozilla Firefox, etc. Once infected, the fake alert of Policeweblab.com claims that the user must have done one of the following things: Copyright and Related Rights Law (Video, Music, Software); Pornographic distribution or viewing abuse; illegal access from victim’s PC without his/her knowledge or consent. As a punishment that is alternative to criminal prosecution, there is an option to pay a fine of $100~$300 via MoneyPak service – by purchasing MoneyPak cash top-up card from Walmart or Kmart. Although the notification claims that the activity of the computer is recorded, and there are videos made to prove the illegal actions of the victim, this is nothing, but a trick used to scare unaware users. No fine has to be paid to unlock the browsers. The only thing that has to be done is to remove the Policeweblab.com virus immediately.
Guide to Remove Videoplusmusic.com Manually and Effectively - Step-by-Step Removal Guide
Videoplusmusic.com is a harmful browser hijacker that shows annoying pop up notification that "FLV Player is recommended (Recommended). Please install to the latest version for best performance" on the PC. It is created by the cyber criminals to distribute adware, Trojan and potentially unwanted programs. Videoplusmusic.com attacks windows operating system and targets all popular web browsers like IE, Firefox and Chrome, etc. this redirect virus is distributed via spam emails, corrupt websites or freeware installation packages. Once it gets inside your system, it will mess up your computer. Since it has ability to alter your browser and register settings, it can take over your web browser and makes the virus to activate itself on the system. If you install software from the given link then you may download enormous threats on your computer. You may not be able to access any of the computer utilities like Task Manager, Registry Editor or others, as all of them might be deactivated. What’s more, Videoplusmusic.com also performs many kinds of malicious tasks on your computer to monitor your online activities. It has ability to escape from the antivirus because it can delete some of your system files as well as it can modify your firewall settings. Videoplusmusic.com may consume all resources making the system performance and internet connection extremely slow. It can completely invade a computer in hidden form without the users’ permission. In order to avoid the more damage, it is important to remove Videoplusmusic.com as quickly as possible.